Ensure that your deviceTRUST contextual security policy has been saved within the deviceTRUST Console and successfully deployed to the host system.
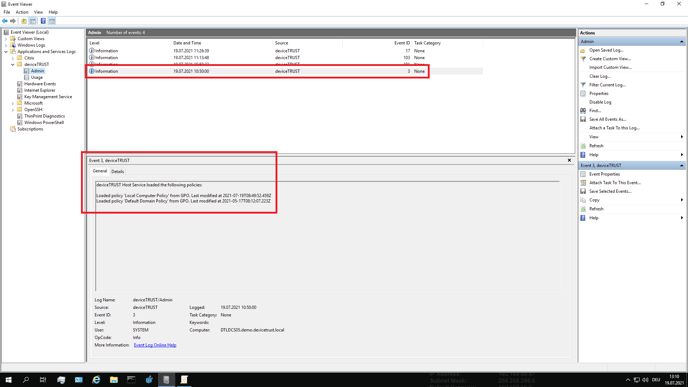
To check which policies are effective, open the Windows Event Log on the remoting or DaaS host system, navigate to APPLICATION AND SERVICE LOGS\DEVICETRUST\ADMIN, and look for Event ID 3, which details the name of each policy and the timestamp that it was last modified.
The deployed policies
- User sessions get their deviceTRUST policies during login and are active until the session is logged out. If newer contextual security policies are deployed on the remoting or DaaS host during this time, they will not affect running user sessions, only new logins.
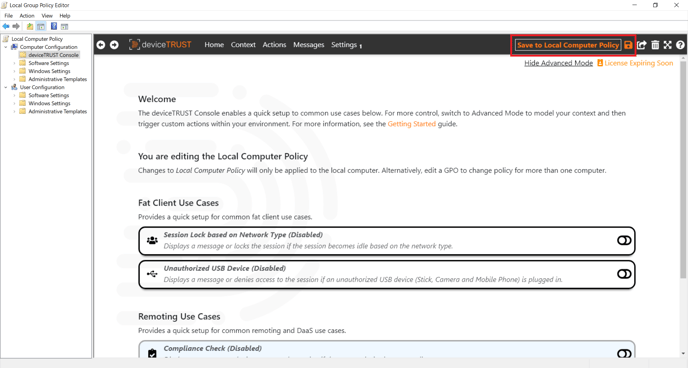
If the policy is not listed or does not have the expected timestamp, ensure that you have successfully saved the policy from within the deviceTRUST Console.
Save the policy
Next, the policy must be successfully deployed to the remoting or DaaS host system. The method used to deploy the policy depends on where the changes were saved.
Local Policy
When using local policy, no additional steps need to be taken to enable the updated contextual security policy for the deviceTRUST Agent.
Group Policy Object (GPO)
When using group policy, a Group Policy update should be forced on the remoting or DaaS host system to propagate an update of the contextual security policy. Of course, waiting for the next group policy refresh is possible, but for testing purposes, this can be forced directly with a call to GPUPDATE /TARGET:COMPUTER. After the updated contextual security policy is successfully deployed to the remoting or DaaS host system, the deviceTRUST Agent will use it immediately.
File-based
When using a file-based policy, the updated contextual security policy is copied to the appropriate target directory as a file-based policy on the remoting or DaaS host system. After the updated file-based contextual security policy is copied to the target directory, the deviceTRUST Agent will use it immediately.